cryptocan
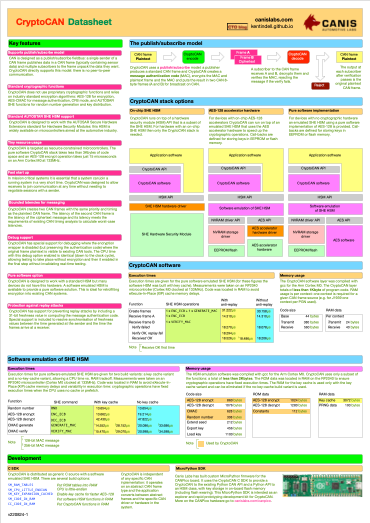
CryptoCAN scheme from Canis Labs is designed to meet the following requirements for CAN communications:
- Fit a publish-subscribe model
- Encrypted messages must have bounded latencies
- Fit within 8-byte CAN frames
- Work on microcontrollers with limited resources
- Support fast-start communications
CryptoCAN takes a standard CAN frame (the plaintext frame) and converts it into a CryptoCAN message (the ciphertext message) that is sent on CAN then converted back into the original plaintext CAN frame by each receiver.
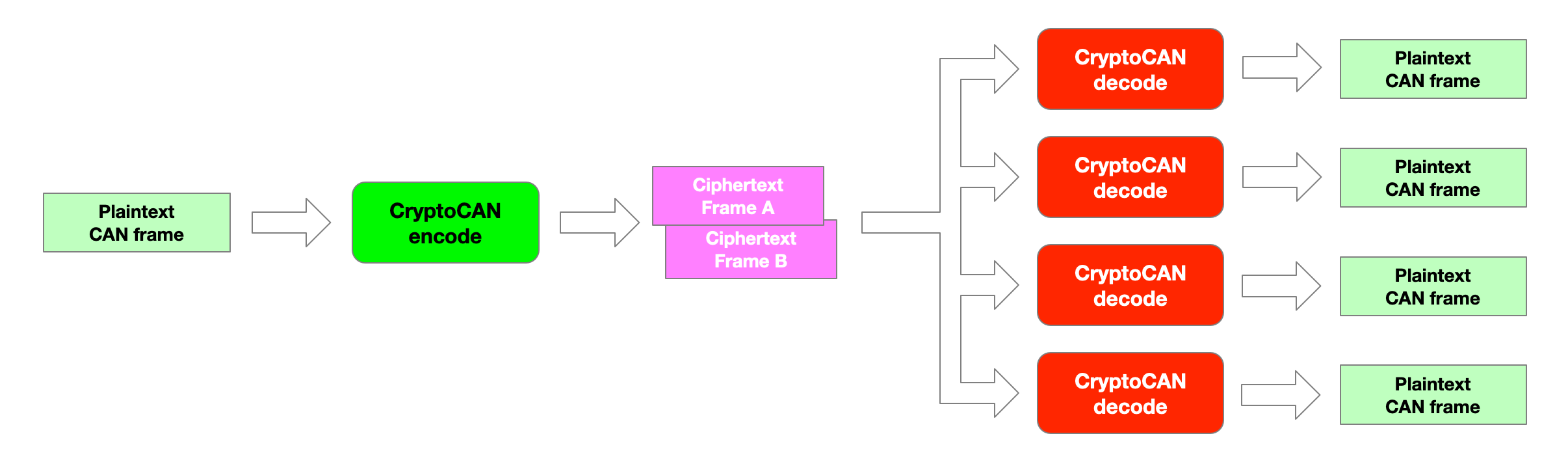
A CAN frame is converted into two CAN frames containing the encrypted original payload and a message authentication code (MAC). These are then decoded back to the plaintext frame at each receiver. The MAC is used to protect the ciphertext message from tampering.
To allow CAN devices using microcontrollers without hardware security modules (HSMs) to participate in secure communications, CryptoCAN has a layered architecture and includes a software emulated HSM.
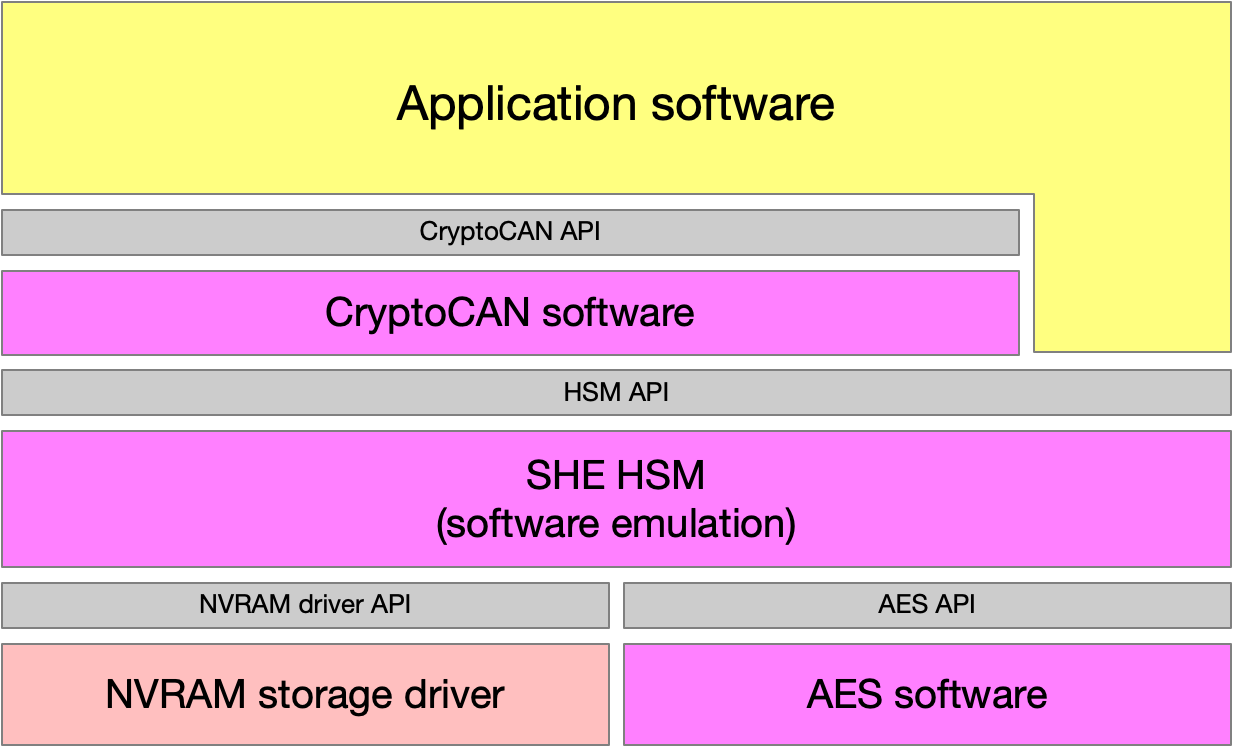
The CryptoCAN stack with an HSM emulated in software and key storage in local non-volatile memory.
The pure software stack is included in MicroPython firmware for the CANPico, with keys stored in the Pico’s flash memory. The CANPico is a platform primarily intended for evaluation and prototyping. Depending on the threat model, the software HSM may be appropriate for deployment.
White paper: Encryption on CAN bus: Overview of CryptoCAN (PDF). Discusses the special requirements for encrypting messages on CAN and gives an overview of CryptoCAN software and how it interfaces to hardware security modules.
CiA newsletter 4/2022 article Securing CAN: Introduction to CryptoCAN (PDF) describing the requirements for any CAN cryptographic scheme and how CryptoCAN meets them.
Our CTO Dr. Ken Tindell gave the talk “Encrypted messaging on CAN bus” at the ASRG 2022 Secure Our Streets conference and the video of the presentation and the slides are available.
GVSETS 2022 conference paper Defending Controller Area Network (CAN) buses (PDF) on the different types of attacks on CAN and techniques to defend against them, including details of CryptoCAN encryption on CAN and the CAN-HG augmentation of CAN for security.
In this second episode of the popular Defending CAN video series our CTO describes the issues of using encryption to defend a CAN bus.
getting started on the canpico
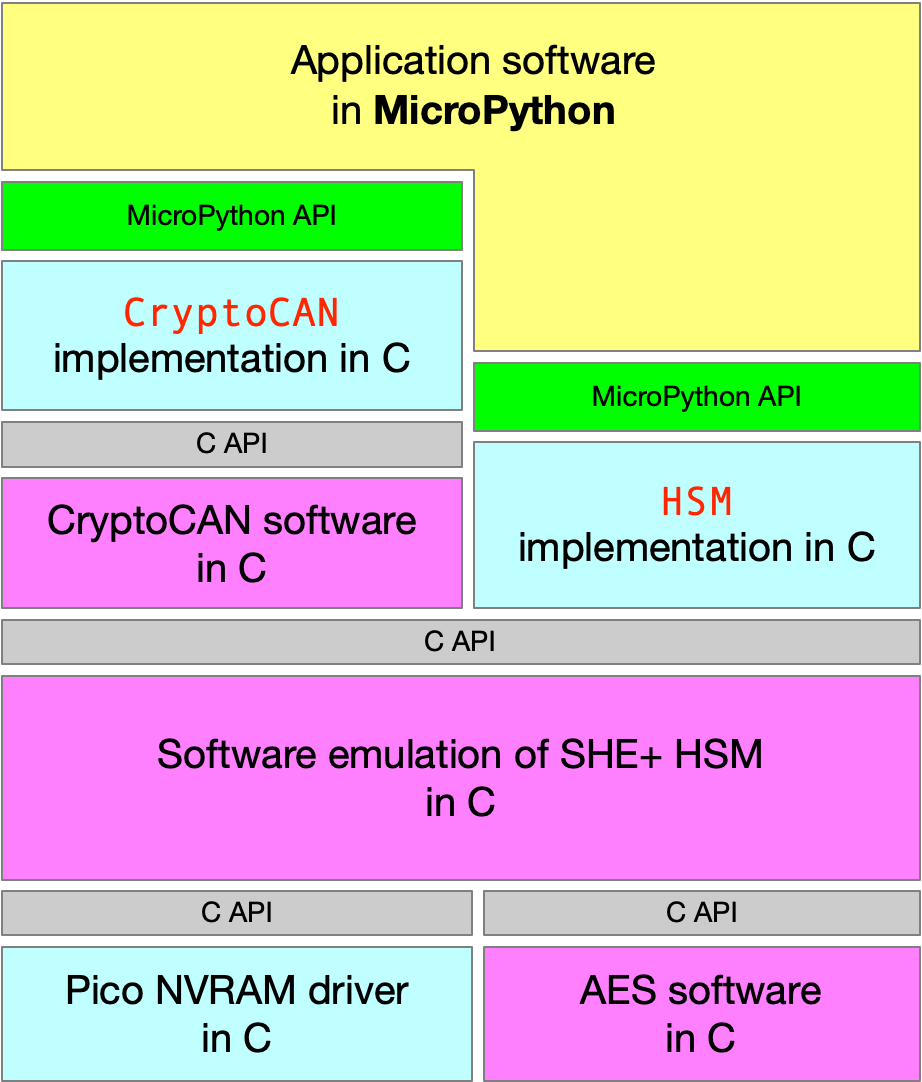
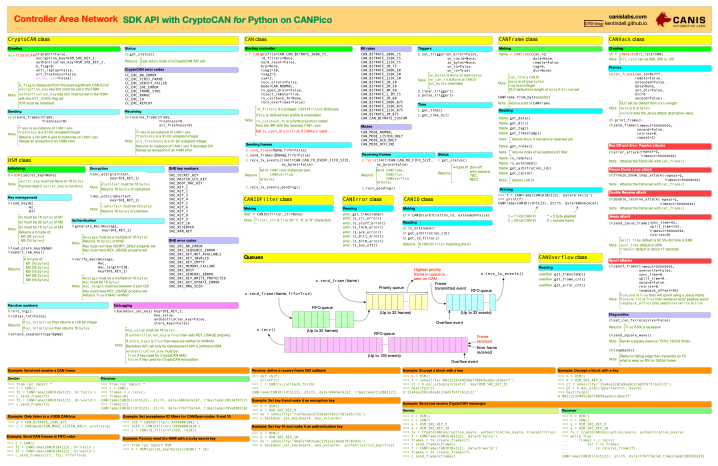
Canis Labs has wrapped the embedded C CryptoCAN stack in a MicroPython implementation. The CryptoCAN stack includes an emulation of an SHE+ HSM using the Raspberry Pi Pico flash chip to store keys. The HSM is made available via a new Python class HSM. The CryptoCAN messaging layer in the stack is made available via the Python CryptoCAN class. The MicroPython firmware with the CryptoCAN stack is available as a free download.
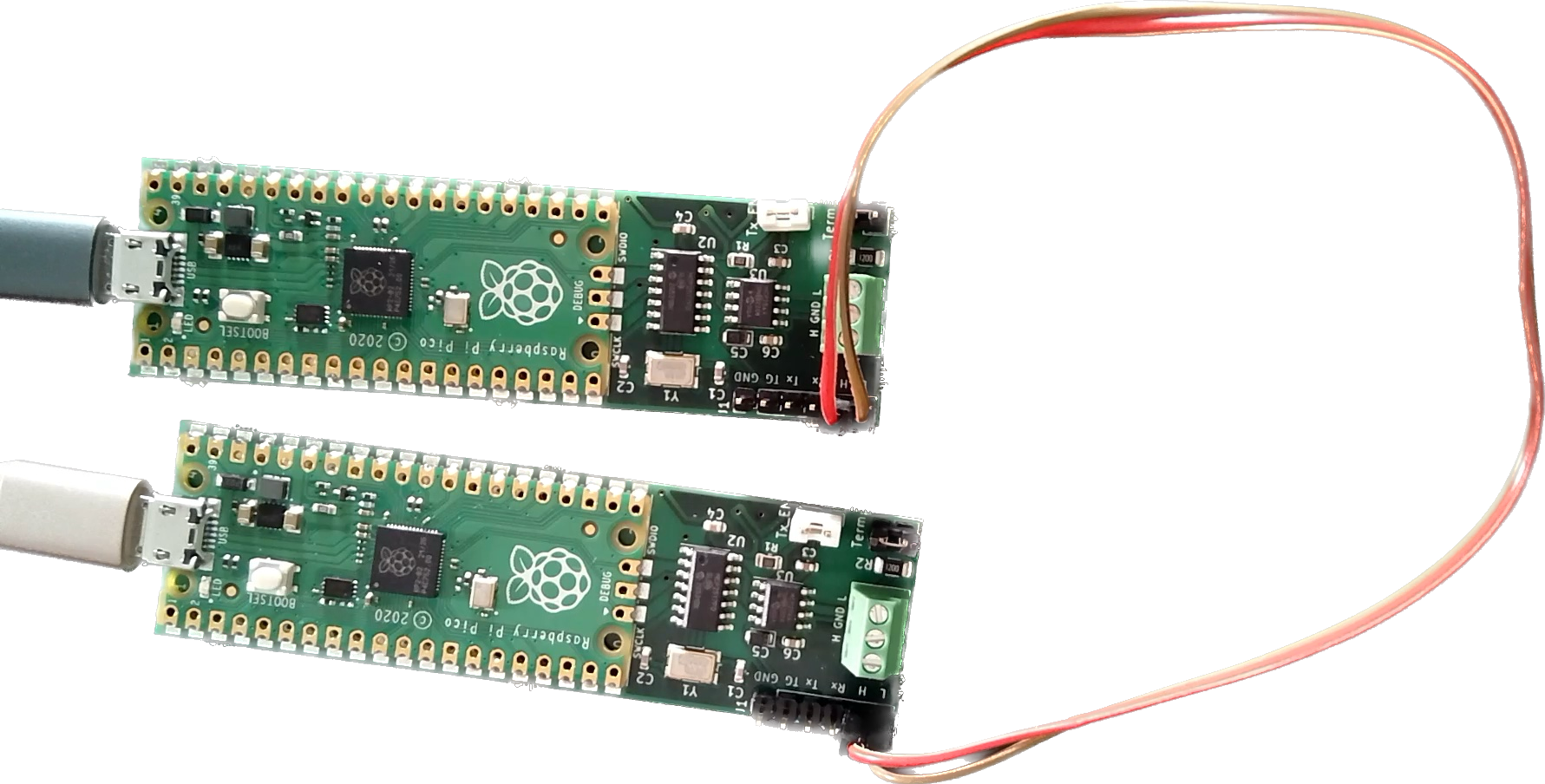
Our CTO has written a quickstart guide on the Canis CTO Blog. It covers setting up the emulated HSM on a Raspberry Pi Pico and creates a tiny CAN bus using two CANPico boards connected together over which encrypted CAN frames are sent.
This video gives a quick introduction to CryptoCAN and how to get started with it on the CANPico with MicroPython. It covers key provisioning with the HSM, how to send encrypted messages over CAN and how to decode them at receivers.
reference documentation
software
Firmware for MicroPython with CAN, CANHack and CryptoCAN APIs for CANPico (firmware-20230309-cc-beta.zip). Firmware is free to use in binary form for the Raspberry Pi Pico under the terms described in LICENSE.txt.